Which framework to choose – Comparing SOC and ISO-27001

What Is ISO 27001?
ISO 27001 is a globally recognized standard for managing information security. It offers a structured framework for developing, operating, maintaining, and continuously enhancing an organization’s Information Security Management System (ISMS). The standard emphasizes safeguarding the confidentiality, integrity, and availability of information by promoting a risk-based approach to identifying and addressing security threats. It also guides the implementation of appropriate controls and the establishment of processes for regular monitoring and improvement. Achieving ISO 27001 compliance reflects an organization’s dedication to information security best practices.

What Is SOC?
A Security Operations Centre (SOC) is a centralized team or facility tasked with continuously monitoring and analysing an organization’s cybersecurity landscape. Its primary role is to detect, investigate, and respond to security threats using a range of tools and technologies. By examining network traffic, log data, and security systems, the SOC works to identify and mitigate potential cyber-attacks, ensuring the ongoing protection and integrity of the organization’s information systems.
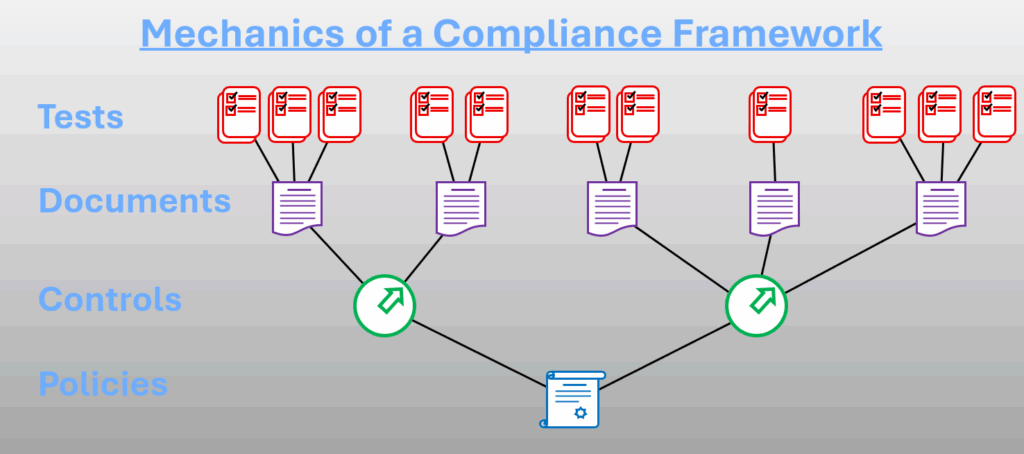
The Mechanics of a Compliance Framework
Although various frameworks may differ in terminology or place emphasis on slightly different aspects, they typically align with the underlying model outlined below. For this example, ISO-27001 will serve as our reference framework.
The standard developed by the International Standards Organisation divides a business into its fundamental activities, each defined by a hierarchy of processes and sub-processes. Ultimately, the framework establishes a set of controls designed to protect and steer these processes.
A business must establish policies that operate within the boundaries defined by those controls. Supporting systems should generate evidence to demonstrate compliance, typically in the form of one or more documents or other forms of measurable evidence, like the unresolved vulnerabilities of a given system.
To ensure ongoing compliance, validation mechanisms should be implemented to verify that the evidence aligns with policy requirements and, by extension, supports the underlying controls.
Vanta will automate cross-referencing policies, controls, documents, and tests. It will track currency of the materials and automate controls around approvals and staff acceptance of certain materials.
How do SOC and ISO 27001 differ?
While both aim to strengthen an organization’s security posture, and ISO 27001 and a Security Operations Centre (SOC) differ in the various facets, touched on below.
Scope
ISO 27001 takes a broad, organization-wide view. It integrates information security principles across people, processes, and technologies, ensuring a unified and systematic approach to managing security risks.
The SOC scope is narrower and functions as an operational unit staffed with analysts and equipped with tools to monitor and address security threats as they arise.
Focus
ISO 27001 is a strategic framework for building and maintaining an Information Security Management System (ISMS). It emphasizes risk assessment, policy creation, control implementation, and continuous improvement.
A SOC, by contrast, is centred on the real-time detection, analysis, and response to security incidents. This includes activities like threat monitoring, incident response, and security event analysis.
Objectives
ISO 27001 aims to develop a robust Information Security Management System (ISMS) that protects the confidentiality, integrity, and availability of information. It also ensures compliance with applicable legal, regulatory, and contractual obligations.
On the other hand, the core goal of a Security Operations Centre (SOC) is to swiftly detect, analyze, and respond to security incidents in order to limit the damage of breaches and safeguard vital assets.
Compliance
ISO 27001 compliance demands a structured approach through the formal implementation of an Information Security Management System (ISMS), as outlined by the standard. This encompasses conducting risk assessments, creating, and enforcing policies, deploying controls, and undergoing periodic audits to validate alignment.
Conversely, SOC compliance does not adhere to a singular standard; instead, it gauges how effectively an organization follows established cybersecurity best practices. SOC operations are often aligned with broader industry frameworks or specific regulatory obligations.
ISO Certification and SOC Reports
ISO independent accreditation bodies authorize and monitor certification bodies to ensure they and their auditors operate according to international norms. JAS-ANZ is the joint Accreditation System of Australia and New Zealand. Auditors of the certification body measure compliance of your implemented ISMS against the standard. SOC uses accredited accountants who measure your incident and response readiness and present a report on their findings. There are three different SOC reports:
- SOC-1 Report focusses om financial systems
- SOC-2 Report focusses on Security, Integrity, Availability, Confidentiality or Privacy and Processing
- SOC-3 is a redacted version of the SOC-2 report for organisation who do not want to disclose their entire SOC-2 report.
SOC-1 and SOC-2 reports can also be produced in Type-1 and Type-2:
- Type-1 reports take a snapshot of the organisation
- Type-2 reports monitor the organisation over a six-month period.
In Summary
Facet | ISO 27001 | SOC |
Scope | Implementation spanning the entire organization | Dedicated organisational function |
Focus | Information Security Management | Active security incident response |
Compliance | Compliance with the ISO standard | Adherence to frameworks, best practice often encouraged by regulations or legislations |
Objectives | Risk management, compliance with a fit for purpose ISMS | Incident discovery, investigation, and response |
Actions | Policy definition, deployment of controls surrounded by risk assessment | Threat awareness and pursuit, incident response, post security event investigation |
Association | A comprehensive ISMS framework | Can technically be part of another framework |
Market | Global orientation | United States oriented |
Certification | ISO 27001-accredited certification body | Licensed CPA (Certified Public Accountant) |
Certificate | Certificate of compliance | Formal attestation |
Period | Three years with intermediate audits at the beginning of years two and three | One year |
Where does GDPR fit into the Framework Landscape
The above discussion would be incomplete without a mention of GDPR.
GDPR takes a somewhat reversed approach towards information security.
The essence of the General Data Protection Regulation (GDPR) lies in its mission to protect the personal data and privacy of individuals within the European Union (EU) and beyond.
GDPR is designed to:
- Give individuals greater control over their personal data.
- Ensure organizations handle data responsibly and transparently.
- Harmonize data protection laws across the EU.
The Seven Key Principles of GDPR
These principles guide how personal data should be held and processed:
- Lawfulness, Fairness, and Transparency
Data must be processed legally, fairly, and in a transparent manner. - Purpose Limitation
Data should be collected for specified, explicit, and legitimate purposes only. - Data Minimization
Only the minimum necessary data should be collected and processed. - Accuracy
Personal data must be accurate and kept up to date. - Storage Limitation
Data should not be kept longer than necessary. - Integrity and Confidentiality
Data must be processed securely to prevent unauthorized access or breaches. - Accountability
Organizations must be able to demonstrate compliance with all principles.
Rights for Individuals
GDPR empowers individuals with rights such as:
- Right to access their data
- Right to rectification
- Right to erasure (“right to be forgotten”)
- Right to data portability
- Right to object to processing
Global Impact
Even non-EU organizations must comply if they handle data of EU residents. Non-compliance can lead to significant fines and reputational damage
Certification Validity
GDPR certification has a maximum validity of three years.
There are intermediate audits, but they are determined by the certification scheme as it applies to your business and the risk profile of your business.

Which framework works best for you?
Ideally, the information above has helped clarify whether ISO 27001 or SOC 2 is a better fit for your organization. While SOC 2 tends to be more cost-effective and simpler to implement, it is generally considered less comprehensive and less rigorous than ISO 27001.
While ISO 27001 requires greater effort to implement and maintain, it offers a more robust framework for safeguarding organizations against information security threats.
The Global Impact statement of GDPR determine whether that standard and its compliance is most suitable. If your organisation handles data of EU citizens, you are legally responsible to be GDPR compliant.
Feel free to connect with our experts—they are here to guide you toward the most suitable solution for your organization and assist you with your implementation.
We empower organizations with innovative expertise in IT governance, IT fleet management, risk management, and compliance—delivering strategic solutions across cyber resilience, data protection, cybersecurity, and business continuity.
